“Networking is an investment in your business. It takes time and when done correctly can yield great results for years to come.”
– Diane Helbig
Network Infrastructure Design & Maintenance
Our Network Infrastructure and Deployment service is designed to build a strong, scalable foundation for your organization’s connectivity needs. From strategic planning to secure implementation, our team ensures that every component of your network is optimized for performance, reliability, and security. With a focus on future-ready design, efficient resource integration, and compliance with industry standards, we deliver an infrastructure that supports your business goals and adapts to evolving demands.
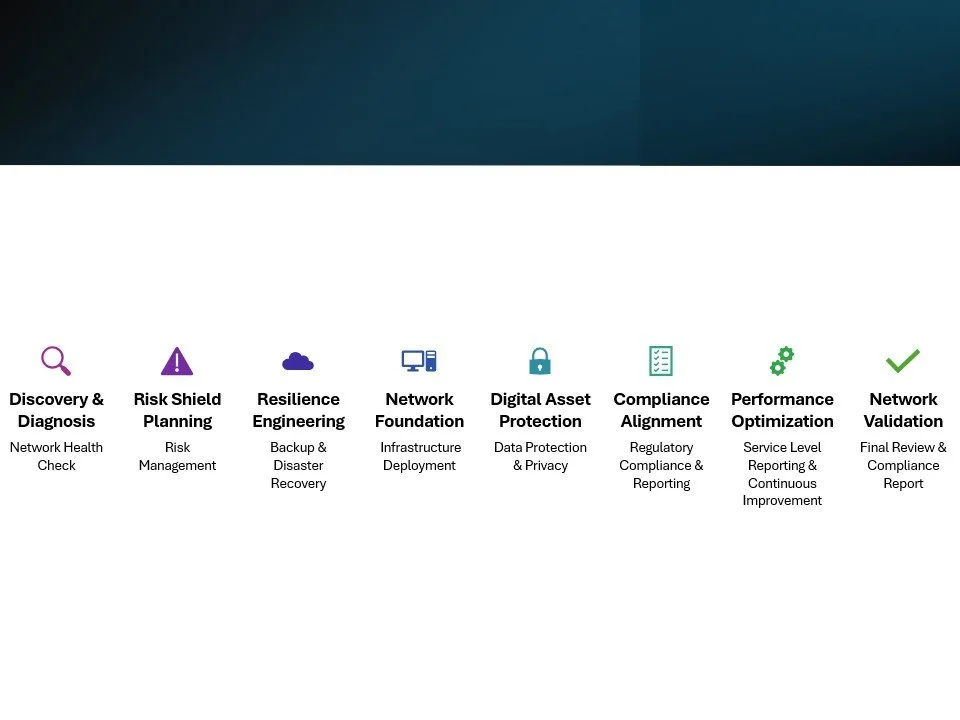
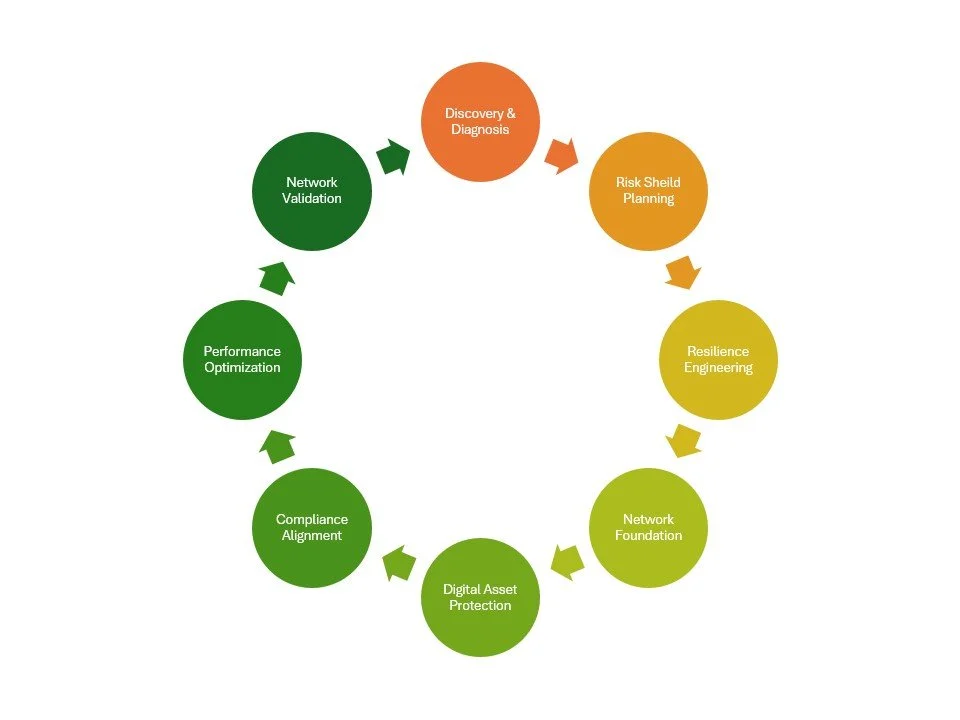
The Golden Network Blueprint
Our Golden Network Blueprint delivers a structured, end-to-end approach to building and optimizing secure, resilient networks. With a focus on thorough assessments, risk management, and compliance, our team of experienced professionals tailors each step to your organization’s specific needs. From initial health checks and risk planning to infrastructure deployment and continuous improvement, we ensure your network not only meets industry standards but also supports your business objectives with enhanced security, reliability, and performance.
-
Our specialists will assess your network’s architecture, devices, and performance, identifying vulnerabilities and inefficiencies. A detailed report will outline the network’s health and key improvement recommendations.
-
Our experts will create a risk management plan, identifying critical risks and implementing security measures like firewalls and access controls. Updated policies and a risk register will support ongoing risk mitigation.
-
Our professionals will design regular backup schedules, establish redundancy systems, and test disaster recovery protocols to ensure resilience. A full backup and recovery plan will be delivered.
-
Our technical team will configure servers, deploy firewalls, and establish secure connections, ensuring effective user access management. Continuous monitoring will validate infrastructure alignment with design specifications.
-
Our data security team will implement encryption and privacy protocols to protect sensitive information and ensure compliance. You will receive a formal data protection policy and compliance documentation.
-
Our compliance specialists will review your network’s adherence to industry standards, applying required controls and preparing necessary reports. Documented procedures and compliance policies will be provided.
-
Our service team will establish SLAs, track performance, and proactively address any issues, while incorporating feedback for continuous improvement. Service level reports and an improvement plan will be delivered.
-
Our assessment team will conduct a thorough review to confirm compliance and design accuracy, resolving any outstanding issues. A comprehensive compliance report will be presented to conclude the engagement.
Frequently Asked Questions
-
How customizable are your network solutions to fit our unique business needs?
Our Network IDM service offering is tailored to meet the unique need of each client. We begin by conducting thorough research to understand your specific business environment and challenges. By engaging with key stakeholders, we gather detailed requirements to ensure our solutions align with your objectives. We then allocate specialized human resources with the expertise required for your project, ensuring a customized approach that addresses your distinct needs and delivers optimal results.
-
What disaster recovery solutions do you implement for network infrastructure?
Our Network IDM service leverages the industry's leading tools and technologies to ensure your network's resilience and continuity. Utilizing robust backup solutions, failover mechanisms such as DNS failover and load balancers, and secure VPN solutions like Cisco AnyConnect and OpenVPN, we provide unparalleled protection for your network.
We also integrate advanced firewalls, manage network configurations, and offer cloud-based disaster recovery. By wielding these powerful resources, we ensure your network is always protected, rapidly recoverable, and optimized for business continuity. -
How do you ensure high performance and reliability of the network?
Our Network IDM service offering ensures high performance and high reliability by leveraging industry-leading best practices and advanced tools. We design scalable, redundant network architectures with robust failover mechanisms and load balancers, to distribute traffic evenly and prevent bottlenecks. Our continuous monitoring and proactive maintenance ensure quick detection and resolution of issues, while configuration management tools automate updates and backups.
-
What are your network management and monitoring capabilities?
Our networking service offering encompasses a comprehensive suite of capabilities designed to ensure optimal performance, security, and compliance. Our risk management strategy includes robust backup and disaster recovery solutions for both production and file servers. In terms of data protection and privacy, we implement advanced firewalls, user access management protocols, secure VPNs for external connections, and meticulous information handling practices. We also address legacy equipment needs, ensuring seamless integration and operation within the network.
Our management of production assets covers a wide range of device types, asset workload balancing, and software in production. Additionally, we adhere to stringent regulatory requirements by providing detailed service level reporting and committing to continuous service level improvement. These capabilities collectively ensure a resilient, secure, and efficient network infrastructure tailored to meet your specific business needs.